What is Shellshock, and How Can You Protect Your Networks?
A new security vulnerability called Shellshock has been discovered. Security experts are already calling it one of the most serious vulnerabilities of all time, even more serious than Heartbleed.
The Shellshock vulnerability is present in Bash, a remote shell commonly used to remotely administer Linux-based systems. This includes many Linux distributions that are used for internet-facing web servers, as well as Mac OSX systems and other “internet of things” devices such as web-enabled video cameras and home automation systems.
The Shellshock vulnerability allows remote code to be injected into environment variables in a Bash session, which is then executed by the target machine.
Remote code injection vulnerabilities like this allow an attacker to take complete control of a remote system, and in the case of Shellshock this can happen with as little as three lines of code.
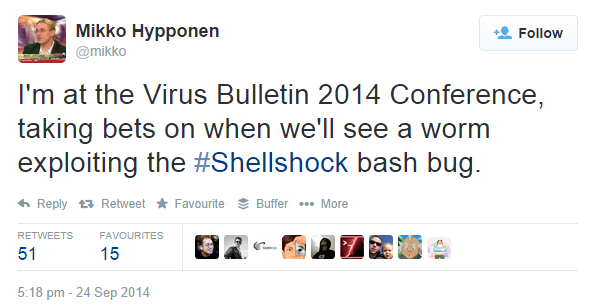
Is Shellshock Being Actively Exploited?
Yes, there are reports that Shellshock is being manually exploited in the wild already. Widespread automated attacks are not yet being seen, but security experts are anticipating attack tools will be developed to locate and exploit Shellshock vulnerable systems on the internet very soon.
Are Microsoft Systems at Risk from Shellshock?
Windows and Windows Server operating systems do not ship with Bash included. So Microsoft systems are not directly at risk unless you’ve deployed a Bash implementation yourself.
However many Windows systems are sitting behind other non-Windows network devices such as firewalls, reverse proxies, and load balancers that may be running a vulnerable implementation of Bash.
How are Vendors Responding to Shellshock?
Your vendor should be providing a fix for any implementations of Bash in their products that are vulnerable to Shellshock.
However, while you wait for your vendors to respond, or if you’ve got other systems that are vulnerable that you do not have any support for (such as web-facing application servers or “roll your own” firewalls) then you will continue to be at risk of an exploit.
How Should You Respond to Shellshock?
An assessment of your systems that are potentially at risk is critical at this stage, before the vulnerability becomes actively exploited at a large scale. Focus on Linux-based systems, especially those that are internet-facing or accessible from outside of your network.
Mitigating Shellshock at the Network Edge
Networks that are protected by an edge security device such as a Palo Alto Networks firewall can rapidly respond to new security vulnerabilities such as Shellshock.
For example, Palo Alto Networks has initiated an emergency IPS content release (a new detection signature) to detect and block the Shellshock exploit.
Other security vendors will also be working to release mitigation for the Shellshock vulnerability, so check with your vendor support or contact an expert IT consultant for advice.
More Reading: